The narrative surrounding the recent incident at the White House dinner—where a man was charged following an alleged assassination attempt on Donald Trump—is a textbook example of reactive journalism. The media is hyper-fixated on a single prop: a knife. They are obsessed with a digital footprint: a photo. This obsession isn’t just lazy; it’s a fundamental misunderstanding of how high-level security actually fails.
Mainstream reports focus on the "shocking" nature of the breach. They treat the individual as an anomaly, a glitch in an otherwise perfect system of protection. This is a lie. If you’ve spent any time analyzing protective intelligence or physical security infrastructure at the federal level, you know that the "lone wolf with a blade" is the smallest variable in the equation.
The real story isn't that a man took a photo with a weapon before an assault. The real story is the catastrophic decay of the Pre-Incident Indicator (PII) filter.
The Knife is a Distraction
Every headline leads with the knife. It’s visceral. It’s scary. It’s also irrelevant. In the world of high-stakes protection, a knife is a low-probability, high-effort tool for a successful assassination. The fixation on the weapon is a way for security agencies to deflect from their actual failure: behavioral detection.
We are taught to look for the object. The TSA looks for the bottle of water; the Secret Service looks for the metal. But objects don't commit acts of violence. Intent does. By focusing on the "what," the security apparatus ignores the "how" and the "why."
I’ve watched security details obsess over hardware while missing the guy in the third row whose pupillary response and gait indicate a high-arousal state. We are spending billions on scanners while our human intelligence—the ability to read a room—is at an all-time low. This man didn't just spawn at the dinner. He moved through a series of checkpoints, digital and physical, that are designed to catch precisely this type of threat. He didn't bypass them; he walked through them because the system is calibrated to look for "terrorists," not "anomalies."
The "Photo Evidence" Fallacy
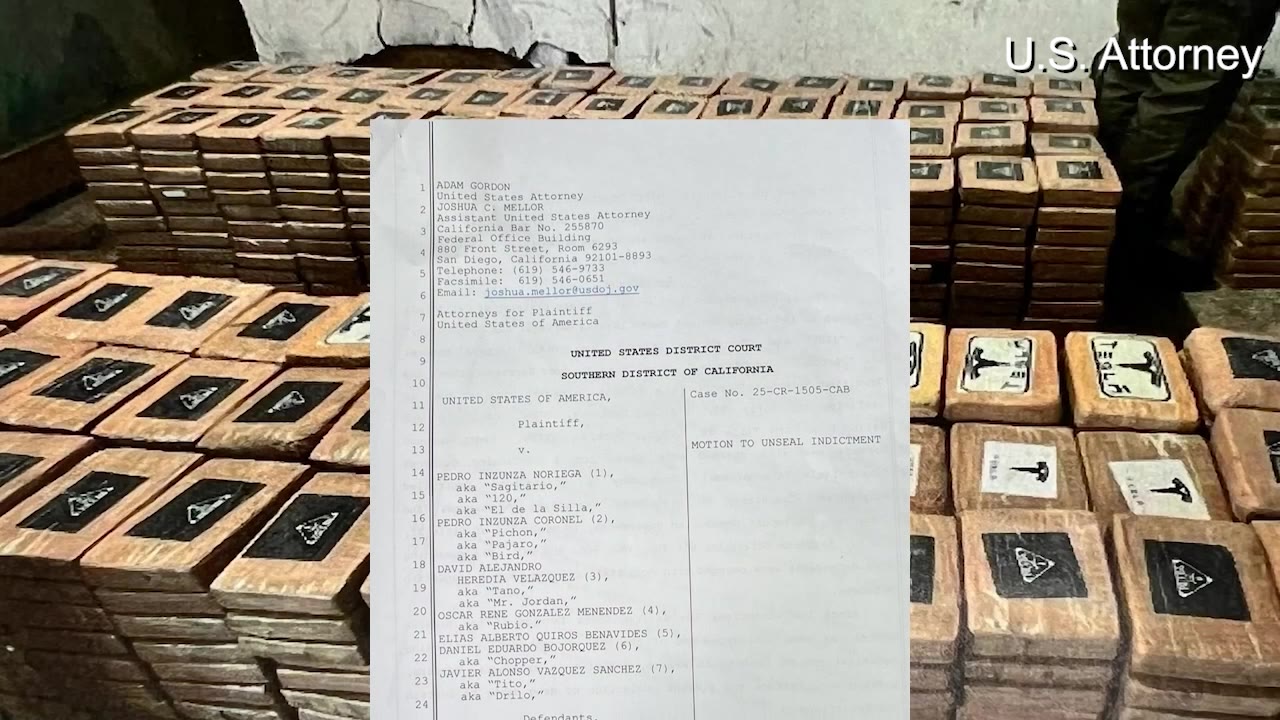
The media is currently parading the "photo with a knife" as a smoking gun. They frame it as a chilling look into the mind of a killer.
Let's be blunt: In 2026, everyone takes photos of everything. Digital bravado is the baseline of modern existence. If the standard for "intent" is a provocative photo on a smartphone, half the population is a suspect.
The "photo before the assault" isn't a breakthrough; it’s a post-hoc justification. Security experts love these photos because they make the failure look inevitable in hindsight. It allows them to say, "Look, the signs were there!" while ignoring the fact that their systems are fundamentally incapable of flagging those signs in real-time.
Reliance on digital forensics after the fact is a participation trophy for law enforcement. It doesn't save lives; it fills out police reports. True security isn't about analyzing a hard drive after the cuffs are on; it's about proactive disruption. We are currently living in a "detect and react" culture when we should be in a "predict and prevent" one.
The White House Isn't a Fortress
The public views the White House as an impenetrable bubble. It’s not. It’s a workplace. It’s a museum. It’s a dinner party venue.
The "White House Dinner Attack" isn't a failure of a fence or a magnetron. It’s a failure of Access Management Logic. When you mix high-profile political figures with donors, staff, and "plus-ones," you create a high-noise environment. Most security breaches aren't the result of "Mission Impossible" style infiltration. They happen because someone didn't check a badge, or someone assumed the guy in the suit belonged there.
The Three Layers of Security Decay
- Credential Inflation: We grant high-level access to too many people. The more "VIPs" you have in a room, the harder it is to track them.
- Technological Over-Reliance: We trust the X-ray more than the agent's intuition. If the machine doesn't beep, the person is "safe."
- The "Normalcy Bias": Agents see thousands of people who look and act exactly like the attacker. The attacker doesn't look like a movie villain; he looks like a bored donor.
Why We Ask the Wrong Questions
People are asking: "How did he get the knife in?"
The better question is: "Why was he allowed within fifty feet of the target?"
If an individual with hostile intent gets close enough to use a knife, the security has already failed three times over. The weapon is just the punctuation at the end of a long sentence of errors.
We need to stop talking about "assassination bids" as if they are lightning strikes—random, unpredictable acts of God. They are logical conclusions to systemic vulnerabilities. When we focus on the individual's "photo" or his "background," we are participating in a narrative of victimization. We are acting as if the Secret Service was "tricked."
They weren't tricked. They were complacent.
The High Cost of the "Lone Wolf" Myth
By labeling every attacker a "lone wolf," we absolve the system of its responsibility. It suggests that this person was so unique, so "off the grid," that no one could have seen him coming.
This is almost never true. Most "lone wolves" are screaming for attention in the digital wilderness for months. The problem isn't a lack of data; it's an inability to filter the signal from the noise. We are drowning in data but starving for intelligence.
If we want to actually protect public figures—regardless of their politics—we have to move past the theater of security. We have to stop patting ourselves on the back for finding a knife after the person has already entered the secure zone.
Stop Looking for the Knife
The fixation on the hardware of the attack is a security theater designed to make the public feel safe. It’s easier to ban knives or install more metal detectors than it is to address the systemic rot in our intelligence-gathering processes.
We are currently defending against the attacks of 1980 with the technology of 2026, while the threats are using the psychology of the future. The "photo with a knife" isn't a clue. It's a symptom of a society that has forgotten that the most dangerous weapon isn't made of steel—it's the person who knows exactly how much noise the system can't hear.
The next breach won't involve a knife. It will involve something even more mundane that the scanners aren't programmed to see. And while the media spends forty-eight hours debating the length of a blade, the real vulnerabilities will remain wide open, waiting for the next person who understands that the "fortress" is actually a stage.
Fire the people who missed the behavior. Stop interviewing the people who found the knife.