The recent accusations from Tehran regarding the use of "copycat" drones by Western intelligence services mark a shift in the theater of plausible deniability. Iran claims that the United States and Israel are deploying unmanned aerial vehicles (UAVs) engineered to mirror the exact electronic signatures and physical silhouettes of Iranian models like the Shahed-136. This is not just a complaint about intellectual property. It is an allegation of a sophisticated "false flag" operation designed to pin the blame for regional strikes on Iranian proxies by using their own technology against them.
For years, the proliferation of Iranian drone technology has been a headache for global security analysts. From the battlefields of Ukraine to the shipping lanes of the Red Sea, the distinctive delta-wing shape of these loitering munitions has become a symbol of asymmetrical warfare. But now, the narrative is flipping. Iranian officials argue that the "Lucas" drones—a name surfacing in intelligence circles to describe these alleged Western clones—are being used to muddy the waters of forensic attribution.
If true, this represents the ultimate irony in modern warfare. The very simplicity and low-cost nature of Iranian drones, which made them so effective at disrupting traditional military hierarchies, now makes them easy targets for duplication.
The Mechanics of Attribution in a Sky Full of Shadows
Attributing a drone strike is rarely about finding a serial number on a scorched wing. In the wreckage of a strike, investigators look for specific patterns in the carbon fiber, the origin of the GPS modules, and the unique frequency hopping patterns of the internal radios. When a drone hits a target, it leaves behind a digital and physical fingerprint.
The Iranian "copycat" theory rests on the idea that the U.S. and Israel have mastered the art of "forensic mirroring." This involves more than just building a drone that looks like a Shahed. It requires sourcing the same off-the-shelf civilian components that Iran uses—often smuggled through complex shell companies—to ensure that the debris matches the expected profile.
If an interceptor downs a drone over a sensitive site, and the resulting wreckage contains the exact same Chinese-made spark plugs and German-designed engines found in Iranian exports, the political fallout is immediate. For Tehran, the fear is that they are being framed for actions they didn't authorize, using tools that look exactly like their own. This creates a "gray zone" of conflict where no one can be certain who pulled the trigger.
The technical challenge of such a feat is immense but not impossible. Military-industrial complexes have long specialized in "Red Teaming"—the practice of building and testing enemy equipment to find weaknesses. Moving from testing enemy equipment to deploying it for clandestine operations is a logical, if ethically murky, progression.
Reverse Engineering the Shahed Success
To understand why the "Lucas" drones are such a potent threat to Iranian diplomacy, one must understand the Shahed's design philosophy. It is essentially a flying lawnmower with a bomb attached. It uses basic internal combustion engines that can be purchased online. Its navigation relies on GNSS signals that are available to anyone.
This lack of proprietary, high-end military tech is Iran's greatest strength and its newest vulnerability.
The Components of a Replica
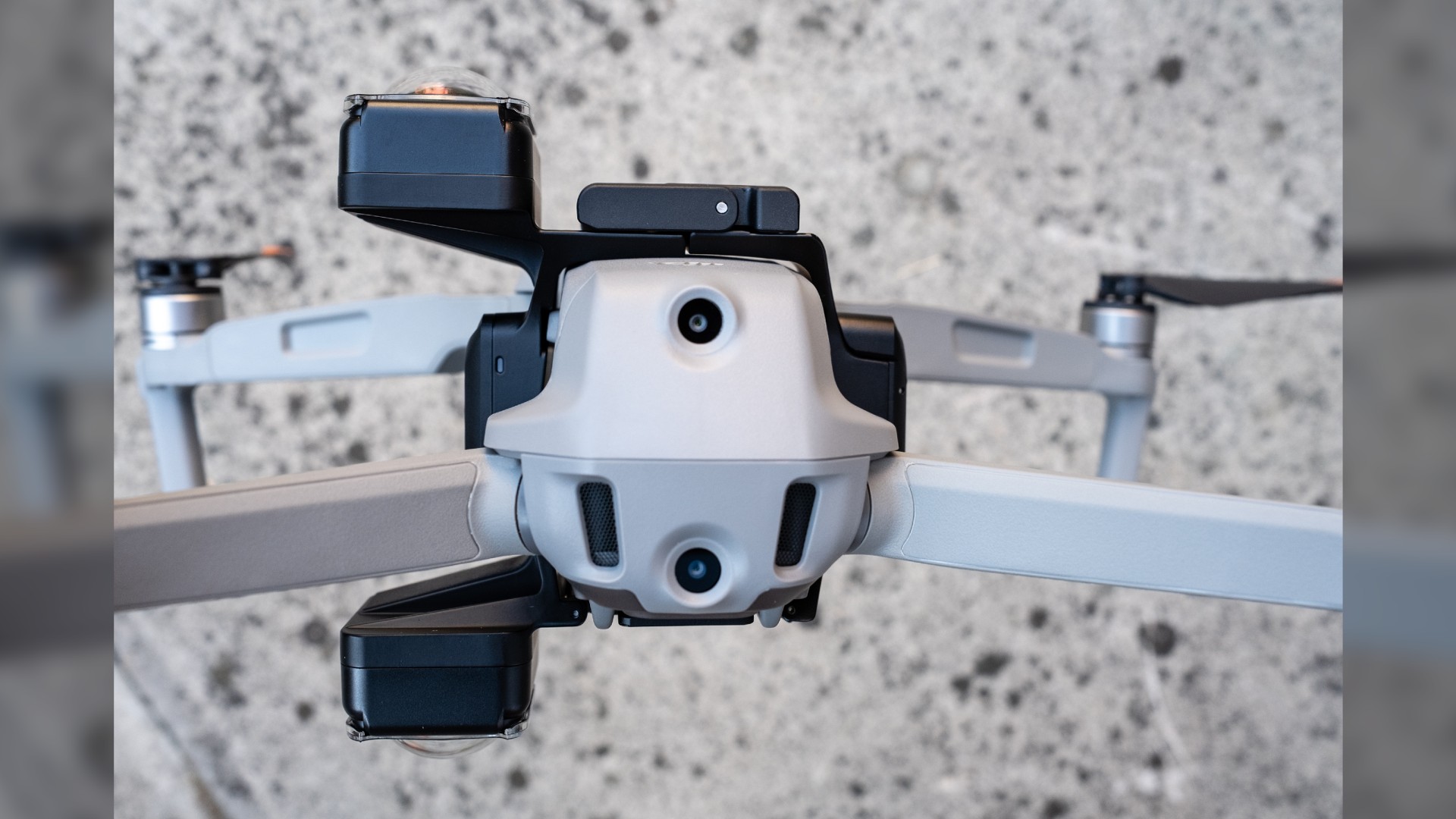
- The Powerplant: Most Iranian loitering munitions use variants of the MD550 engine. These are widely available in the hobbyist and agricultural markets. A state-level actor could easily mass-produce or acquire these to ensure the acoustic signature of the drone matches the Iranian original.
- The Airframe: Delta-wing designs are aerodynamically stable and simple to mold. Using similar resin and fiberglass compositions makes the wreckage look identical under microscopic analysis.
- The Logic Board: This is where the real deception happens. By mimicking the flight control software and the specific way the drone "handshakes" with its controllers, a clone can fool electronic warfare suites into identifying it as a known Iranian threat.
When these elements are combined, the resulting craft is virtually indistinguishable from the original during a high-stress engagement. A radar operator sees a blip with the expected RCS (Radar Cross Section). A thermal sensor sees the expected heat signature. After the explosion, the metal fragments tell a story that points directly back to Tehran.
The Strategic Logic of the Frame Job
Why would a superpower bother cloning a "budget" drone? The answer lies in the avoidance of escalation. If the U.S. or Israel uses a Predator or a Reaper to take out a target, there is no denying who was responsible. That act carries a specific weight in international law and diplomatic relations.
However, if a "Shahed" hits a target, the narrative shifts to Iranian aggression. It justifies sanctions. It rallies allies. It provides a casus belli that is much easier to sell to a skeptical global public. This is the "war of narratives" where the weapon is less important than the identity of the perceived shooter.
There is historical precedent for this kind of technological masquerade. During the Cold War, both sides frequently captured and evaluated each other's hardware, occasionally using it in ways that blurred the lines of origin. The difference now is the scale and the speed of the information cycle. A photo of a crashed drone on Twitter can trigger a diplomatic crisis in minutes.
The Counter Argument and the Burden of Proof
While Iran’s claims are strategically convenient for their defense, they face a massive credibility gap. Western intelligence agencies argue that Iran is simply trying to escape accountability for its proliferation of weapons to non-state actors. The "copycat" narrative serves as a pre-packaged excuse for every time an Iranian drone is found where it shouldn't be.
Critics point out that the logistics of running a parallel production line for "enemy" drones would be incredibly inefficient. Why spend millions to perfectly replicate a cheap drone when you have much better technology at your disposal? The counter-argument from Tehran is that the "efficiency" is not found in the strike itself, but in the political outcome.
Evidence of these clones remains elusive. We have seen grainy footage and photos of debris, but nothing that proves a Western origin for a "Shahed-style" craft. However, the absence of evidence is not evidence of absence in the world of black-budget operations. The mere existence of the "Lucas" drone rumor has already achieved a specific goal: it has introduced a seed of doubt into every future attribution.
Disruption of the Global Defense Market
This development is sending ripples through the defense industry. If a nation’s "signature" weapon can be cloned and used against them as a psychological operation, the value of that weapon changes. We are moving toward a period where "authentication" will be as important as "stealth."
Future drone systems will likely include encrypted, tamper-proof hardware "tags" that prove their origin, similar to how high-end luxury goods use blockchain to fight counterfeits. Without these digital watermarks, the sky becomes a chaotic space where any actor can wear the mask of another.
Small nations that previously saw drones as a way to punch above their weight are now realizing they might be handing their enemies a convenient disguise. The democratization of flight has led to a crisis of identity.
The New Rules of Engagement
- Forensics First: Intelligence agencies must now look for "anomalous similarities"—parts that are too identical to the original, suggesting a deliberate attempt to match a profile.
- Electronic Fingerprinting: Tracking the specific radio frequency (RF) noise emitted by the drone's components, which is harder to fake than the physical shape.
- Supply Chain Intelligence: Monitoring the global flow of the specific civilian parts used in these drones to see if unexpected "black holes" appear in the market.
This isn't just about drones anymore. It's about the erosion of truth in the theater of war. When a piece of hardware can no longer be trusted to tell the story of who launched it, the very nature of deterrence changes. You cannot deter an enemy who can hide behind your own face.
The reality of the "Lucas" drone—whether it is a widespread operational tool or a niche psychological tactic—matters less than the fact that the accusation is now a permanent part of the geopolitical landscape. The next time a delta-wing drone strikes a sensitive target, the first question won't be "Where did it come from?" but "Whose mask was it wearing?"
The sky is getting crowded, and the shadows are getting longer. In this environment, the most dangerous weapon isn't the one that hits the hardest, but the one that leaves the most confusing trail. We have entered the era of the "doppelgänger defense," and the traditional rules of the game no longer apply.
Track the shifts in drone manufacturing hubs across Southeast Asia and Eastern Europe to see where the next generation of "neutral" components is being sourced.